This chapter provides a brief summary of the
background and functions of POSIX ACLs for
Linux file systems. Learn how the traditional
permission concept for file system objects can be expanded
with the help of ACLs (Access Control Lists) and
which advantages this concept provides.
Note
[POSIX ACLs]The term ``POSIX ACL'' suggests that this is a
true POSIX (Portable Operating System Interface) standard.
The respective draft standards POSIX 1003.1e and POSIX 1003.2c have
been withdrawn for several reasons. Nevertheless, ACLs as found on
many systems belonging to the UNIX family are based on these
documents and the implementation of file system ACLs as described
in this chapter follows these two standards as well. They
can be viewed at
http://wt.xpilot.org/publications/posix.1e/
Traditionally, a file object in Linux is associated with three sets of permissions. These sets includes the read (r), write (w), and execute (x) permissions for each on of three types of users -- the file owner, the group, and other users. In addition to that, it is possible to set the set user id, set group id, and the sticky bit. A more detailed discussion of this topic can be found in the section Users and Access Permissions of the User Guide.
This lean concept is fully adequate for most practical cases. However, for more complex scenarios or advanced applications, system administrators formerly had to use a number of tricks to circumvent the limitations of the traditional permission concept.
ACLs can be used for situations that require an extension of the traditional file permission concept. They allow assignment of permissions to individual users or groups even if these do not correspond to the original owner or the owning group. Access Control Lists are a feature of the Linux kernel and are currently supported by ReiserFS, Ext2, Ext3, JFS, and XFS. Using ACLs, complex scenarios can be realized without implementing complex permission models on the application level.
The advantages of ACLs are clearly evident in situations such as the replacement of a Windows server by a Linux server. Some of the connected workstations may continue to run under Windows even after the migration. The Linux system offers file and print services to the Windows clients with Samba.
Given than Samba supports access control lists, user permissions can be configured both on the Linux server and in Windows with a graphical user interface (only Windows NT and later). With winbindd, it is even possible to assign permissions to users that only exist in the Windows domain without any account on the Linux server. On the server side, edit the Access Control Lists using getfacl and setfacl.
The following section explains the basic structure of an ACL and its various characteristics. The interrelation between ACLs and the traditional permission concept in the Linux file system is briefly demonstrated by means of several figures. Two examples show how you can create your own ACLs using the correct syntax. In conclusion, find information about the way ACLs are interpreted by the operating system.
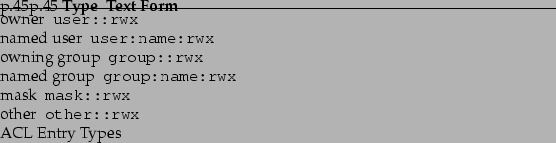
There are two basic classes of ACLs: A minimum ACL merely comprises the entries for the types owner, owning group, and other, which correspond to the conventional permission bits for files and directories. An extended ACL goes beyond this. It must contain a mask entry and may contain several entries of the named user and named group types. Table B.1 provides a summary of the various types of ACL entries that are possible.
The permissions defined in the entries owner and other are always effective. Except for the mask entry, all other entries (named user, owning group, and named group) can be either effective or masked. If permissions exist in one of the above-mentioned entries as well as in the mask, they are effective. Permissions contained only in the mask or only in the actual entry are not effective. The example in Table B.2 demonstrates this mechanism.
Figure B.1 and Figure B.2 illustrate the two cases of a minimum ACL and an extended ACL. The figures are structured in three blocks -- the left block shows the type specifications of the ACL entries, the center block displays an example ACL, and the right block shows the respective permission bits according to the conventional permission concept as displayed by ls -l, for instance.
In both cases, the owner class permissions are mapped to the ACL entry owner. Equally, other class permissions are mapped to the respective ACL entry. However, the mapping of the group class permissions is different in both cases:
This mapping approach ensures the smooth interaction of applications with ACL support and those without ACL support. The access permissions that were assigned by means of the permission bits represent the upper limit for all other ``fine adjustments'' made by means of ACLs. All permissions not reflected here were either not set in the ACL or are not effective. If permission bits are changed, this is also reflected in the respective ACL and vice versa.
The handling of access ACLs is demonstrated in three steps by means of the following example:
The command umask 027 sets the default permissions by giving the owner the full range of permissions (0), denying the group write access (2), and giving other users no permissions at all (7). umask actually masks the corresponding permission bits or turns them off. For details, consult the corresponding man page (man umask).
This should create the mydir directory with the default permissions as set by umask. Use the following command to check if all permissions were assigned correctly:
# file: mydir
# owner: tux
# group: project3
user::rwx
group::r-x
other::---
The output of getfacl precisely reflects the mapping of permission bits and ACL entries as described in B. The first three output lines display the name, owner, and owning group of the directory. The next three lines contain the three ACL entries owner, owning group, and other. In fact, in the case of this minimum ACL, the getfacl command does not produce any information you could not have obtained with ls.
Your first modification of the ACL is the assignment of read, write, and execute permissions to an additional user jane and an additional group djungle.
The option -m prompts setfacl to modify the existing ACL. The following argument indicates the ACL entries to modify (several entries are separated by commas). The final part specifies the name of the directory to which these modifications should be applied.
Use the getfacl command to take a look at the resulting ACL.
# file: mydir
# owner: tux
# group: project3
user::rwx
user:jane:rwx
group::r-x
group:djungle:rwx
mask::rwx
other::---
In addition to the entries initiated for the user jane and the group djungle, a mask entry has been generated. This mask entry is set automatically to reduce all entries in the group class to a common denominator. Furthermore, setfacl automatically adapts existing mask entries to the settings modified, provided you do not deactivate this feature with -n. mask defines the maximum effective access permissions for all entries in the group class. This includes named user, named group, and owning group. The group class permission bits that would be displayed by ls -dl mydir now correspond to the mask entry.
The first column of the output now contains an additional + to indicate that there is an extended ACL for this item.
Edit the mask entry with setfacl or chmod.
drwxr-x---+ ... tux project3 ... mydir
# file: mydir
# owner: tux
# group: project3
user::rwx
user:jane:rwx # effective: r-x
group::r-x
group:djungle:rwx # effective: r-x
mask::r-x
other::---
After executing the chmod command to remove the write permission from the group class bits, the output of the ls command is sufficient to see that the mask bits must have changed accordingly: write permission is again limited to the owner of mydir. The output of the getfacl confirms this. This output includes a comment for all those entries where the effective permission bits do not correspond to the original permissions, because they are filtered according to the mask entry. Of course, the original permissions can be restored at any time with chmod:
drwxrwx---+ ... tux project3 ... mydir
# file: mydir
# owner: tux
# group: project3
user::rwx
user:jane:rwx
group::r-x
group:djungle:rwx
mask::rwx
other::---
Directories can be equipped with a special kind of ACL -- a default ACL. The default ACL defines the access permissions all objects under this directory inherit when they are created. A default ACL affects subdirectories as well as files.
There are two different ways in which the permissions of a directory's default ACL are handed down to the files and subdirectories in it:
All system calls that create file system objects use a mode parameter that defines the access permissions for the newly created file system object:
The following three examples show the main operations for directories and default ACLs:
The option -d of the setfacl command prompts setfacl to perform the following modifications (option -m) in the default ACL.
Take a closer look at the result of this command:
# file: mydir
# owner: tux
# group: project3
user::rwx
user:jane:rwx
group::r-x
group:djungle:rwx
mask::rwx
other::---
default:user::rwx
default:group::r-x
default:group:djungle:r-x
default:mask::r-x
default:other::---
getfacl returns both the access ACL and the default ACL. The default ACL is formed by all lines that start with default. Although you merely executed the setfacl command with an entry for the djungle group for the default ACL, setfacl automatically copied all other entries from the access ACL to create a valid default ACL. Default ACLs do not have an immediate effect on access permissions. They only come into play when file system objects are created. These new objects inherit permissions only from the default ACL of their parent directory.
# file: mydir/mysubdir
# owner: tux
# group: project3
user::rwx
group::r-x
group:djungle:r-x
mask::r-x
other::---
default:user::rwx
default:group::r-x
default:group:djungle:r-x
default:mask::r-x
default:other::---
As expected, the newly-created subdirectory mysubdir has the permissions from the default ACL of the parent directory. The access ACL of mysubdir is an exact reflection of the default ACL of mydir, just as the default ACL that this directory will hand down to its subordinate objects.
-rw-r-----+ ... tux project3 ... mydir/myfile
# file: mydir/myfile
# owner: tux
# group: project3
user::rw-
group::r-x # effective:r--
group:djungle:r-x # effective:r--
mask::r--
other::---
Important in this example: touch passes on mode with the value 0666, which means that new files are created with read and write permissions for all user classes, provided no other restrictions exist in umask or in the default ACL (see B).
If effect, this means that all access permissions not contained in the mode value are removed from the respective ACL entries. Although no permissions were removed from the ACL entry of the group class, the mask entry was modified to mask permissions not set via mode.
This approach ensures the smooth interaction of applications, such as compilers, with ACLs. You can create files with restricted access permissions and subsequently mark them as executable. The mask mechanism makes sure that the respective users and groups are assigned the permissions they are granted in the default ACL.
The following section provides brief information on the check algorithm applied to all processes or applications before they are granted access to an ACL-protected file system object. As a basic rule, the ACL entries are examined in the following sequence: owner, named user, owning group or named group, and other. The access is handled in accordance with the entry that best suits the process; permissions do not accumulate.
Things are more complicated if a process belongs to more than one group and would potentially suit several group entries. An entry is randomly selected from the suitable entries with the required permissions. It is irrelevant which of the entries triggers the final result ``access granted''. Likewise, if none of the suitable group entries contains the correct permissions, a randomly selected entry triggers the final result ``access denied''.
As described in the preceding sections, ACLs can be used to implement very complex permission scenarios that meet the requirements of modern applications. The traditional permission concept and ACLs can be combined in a smart manner. However, some important applications still lack ACL support. Except for the star archiver, there are currently no backup applications that guarantee the full preservation of ACLs.
The basic file commands (cp, mv, ls, and so on) do support ACLs, but many editors and file managers (such as Konqueror) do not. When copying files with Konqueror, for instance, the ACLs of these files are lost. When modifying files with an editor, the ACLs of files are sometimes preserved, sometimes not, depending on the backup mode of the editor used:
With (hopefully) more ACL-enabled applications released over time, Linux systems will be able to benefit from this feature to the full extent.
Tip
[Additional Information]Detailed information about ACLs is
available at the following URLs:
http://sdb.suse.de/en/sdb/html/81_acl.html
http://acl.bestbits.at/
and in [1]getfacl, [5]acl, and [1]setfacl.